Chris Boyd cboyd at gizmopartners.com Wed Jul 31 15:50:09 UTC 2013
I would guess that it's becasuse many VPN services still support PPTP which can be attacked as outlined here:
Academic: Cryptanalysis of Microsoft's PPTP Authentication Extensions (MS-CHAPv2) - Schneier on Security--Chris
That link doesn't even mention the worst vulnerability in PPTP/MS-CHAPv2. Strangely, it's only in the PDF version http://www.schneier.com/paper-pptpv2.pdf at the bottom of page 6:
Note also that the MS-CHAP response generation algorithm is also a weak
link, even when passwords contain adequate entropy. It is clear that the NT
hash can be recovered with just two DES exhaustive keysearches (about 256
trial DES decryptions on average)
In other words, PPTP/MS-CHAPv2 is equivalent to encrypting your password with *single DES* and sending it over the untrusted network. It doesn't matter how strong your plaintext password is. Not only can the passive eavesdropper decrypt your VPN-tunneled data, he can obtain the NT hash which is a password-equivalent credential allowing him to impersonate the user to log into any other network services.
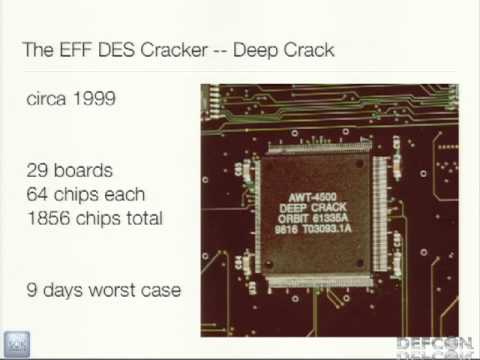
Moxie Marlinspike and David Hulton described the exploit for it at Defcon 20 last summer:
Defeating PPTP VPNs and WPA2 Enterprise with MS-CHAPv2
Moxie's Cloudcracker online service will decrypt your PPTP packet captures using an FPGA cluster from Pico Computing. Last I heard, the price was a flat fee of $200, although it sometimes goes on sale.
A death blow for PPTP - The H Security: News and Features The H: Open Source, Security and Development
So it's not just the NSA, it's any passive observer with a budget of $200 for a one-off or ~$10K for their own hardware capability.
PPTP is old and busted, don't let your friends use it! If you've ever used it, change your password. IMHO, if there's any other protocol more deserving of the "internet kill switch" I don't know what it is.
- Marsh
(sorry for not threading properly, I just subscribed to reply)